In this tutorial, you’ll learn how to find the user’s last logon time using different methods. You can use any of these methods to determine an Active Directory user’s last sign-in date and time.
As a system administrator, there are many situations in which you want to find the user’s last logon date and time. You may probably want to audit any activity or gather all the inactive users in Active Directory over a period of time, etc.
There are numerous third-party software programs available that can help you determine a user’s last logon time. However, many people opt not to use these programs because they typically demand a license. Even if some of them are free, they have certain limitations. These programs must communicate with your Active Directory to retrieve information, and some businesses do not utilize it for security reasons.

What is LastLogonTimeStamp in Active Directory?
The purpose of the LastLogonTimeStamp is to help identify stale user and computer accounts. Administrators can use the lastLogontimeStamp attribute to determine if a user or computer account has recently logged onto the domain.
What is the difference between LastLogon and LastLogonTimeStamp?
The lastlogon attribute is the most accurate way to check active directory users last login time. Lastlogon is only updated on the domain controller that performs the authentication and is not replicated. Whereas LastLogontimestamp is replicated, but by default only if it is 14 days or older than the previous value.
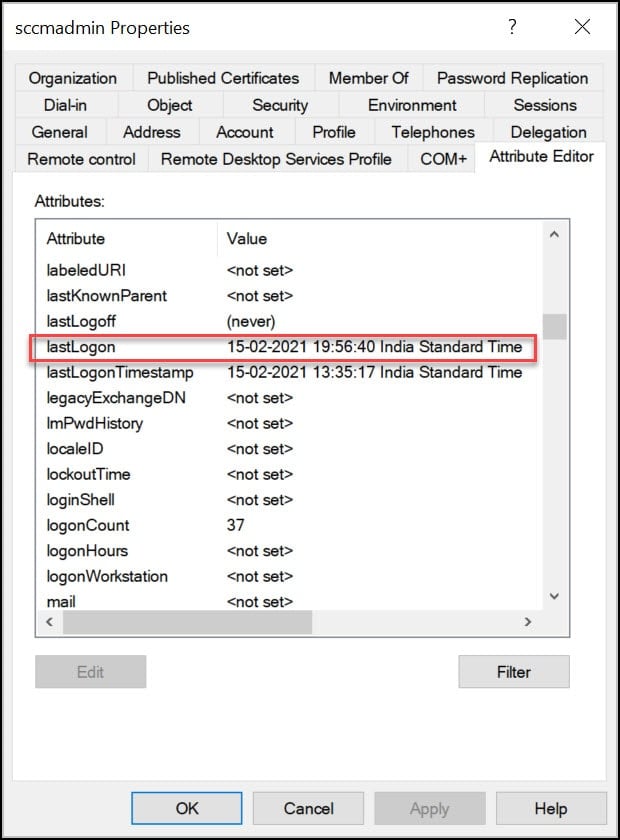
Method 1: Find the user’s logon time in Active Directory
Finding the last logon time of a user is pretty simple using Active Directory.
- Login to a Domain Controller.
- Launch Active Directory Users and Computers console (dsa.msc).
- Click View and ensure Advanced features is turned on.
- On the left pane, click Users and select any user, right click the user account and click Properties.
- In the list of attributes, look for lastLogon. This attribute shows the time the user was last logged in the domain.
Method 2: Find User’s last logon time using CMD
Using the command prompt, you can find the last logon time of the user. You don’t need a domain admin account to get AD user information.
- Click Start and launch the command prompt.
- Run the command: net user username /domain| findstr “Last”
- The CMD output shows the user’s last logon time and date.

Method 3: Find User Last Logon time using PowerShell
You can find the user logon date and time using PowerShell command. You can run the below command either on a domain controller or a member server.
- Log in to a Domain Controller.
- Import the Active Directory PowerShell module, Import-Module ActiveDirectory.
- Run the below PowerShell command to find the user’s login time with date.
Get-ADUser -Identity "username" -Properties LastLogon
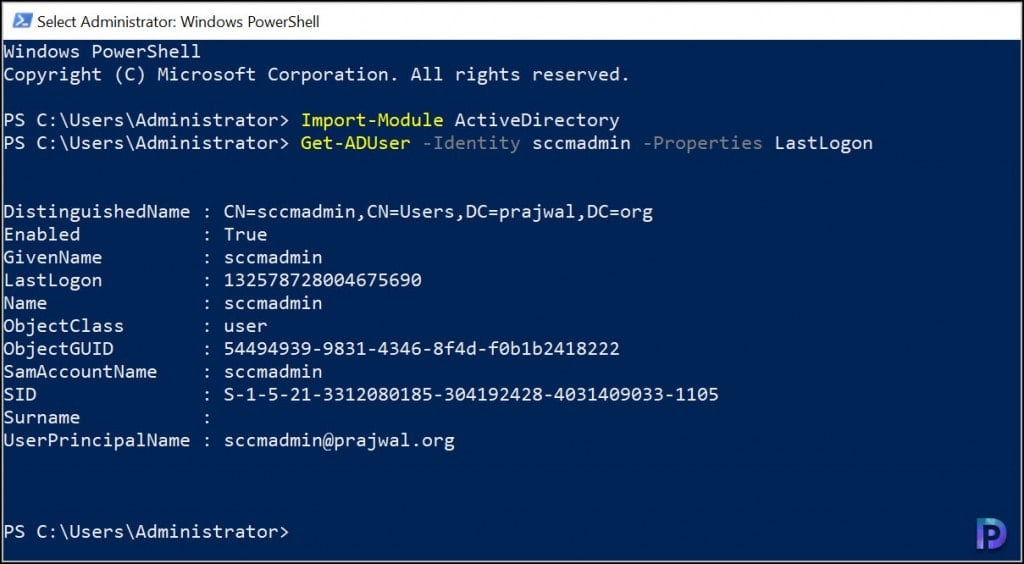
When you run the above command, notice that Lastlogon value is in a different format. It’s in a timestamp format and you need to convert the value to a readable format. Use the below command to convert the value to normal time. Do not forget to replace the user name with your username.
Get-ADUser -Filter {Name -eq "username"} -Properties * | Select-Object Name, @{N='LastLogon'; E={[DateTime]::FromFileTime($_.LastLogon)}}

Method 4: Find last Logon Time of User using SCCM
From the SCCM console, you can find the previous logon time of the user account. SCCM uses Active Directory to fetch the information when you run the discovery methods. Discovery creates a discovery data record (DDR) for each discovered object and stores this information in the SCCM database.
There are two prerequisites before you use SCCM to find the logon time of a user:
- You should have enabled the SCCM discovery methods before you intend to determine the user logon details. The Active Directory user discovery method must be enabled.
- On the Active Directory user discovery properties, ensure lastLogon and lastLogonTimestamp attributes are enabled for discovery.
To find the last logon time of a user using SCCM, follow the below steps.
- Launch the Configuration Manager console.
- Navigate to Assets and Compliance\Overview\Users\All Users.
- Search for the user account and right-click the User object.
- On the user properties box, click General tab.
- The LastLogon attribute should reveal the last logon time of a user account.

Method 5: Find user sign-in activity in Microsoft 365 admin center
In the Microsoft 365 admin center, an administrator can view the times a user manually signed in with their username and password in the past 30 days. The user sign-in activity details include the date and time of the login, status and failure reason.
To view the user’s last logon date and time in Microsoft 365 admin center:
- Sign in to the Microsoft 365 admin center.
- Expand Users > Active Users and select a user.
- On the User properties window, under Last sign-in, select View last 30 days.
- The sign-in activity screen shows the user’s last logon date and time for the past 30 days.

Method 6: Find user’s last login details in Intune
If your organization manages Windows devices using Intune, you can find the user’s last login details in the Intune admin center. Sign in to the Intune admin center and go to Users. From the list of users, select a user and now click on Sign-in logs. Here, you can see the date and time of the user’s login, including the user’s location, IP address, and request ID.
To export the user’s sign information, you can click on the Download button. The file can be exported in JSON and CSV formats.





What cmd prompt or powershell script can I user to check when a user last logged into a specific computer?
Hello Prajwal,
How to find 10k machines’ last login time?
I think we have to use CMPivot or some other tools to get this done.
To run a PowerShell script to run Lastlogon and email the results and use the speech synthesizer to read out results try :
Get-ADUser -Filter * -Properties lastLogon | Select samaccountname, @{Name=”lastLogon”;Expression={[datetime]::FromFileTime($_.’lastLogon’)}} > C:\temp\lastlogin.csv
$From = “me@domain.org”
$To = “me@domain.org”
$Attachment = “C:\Temp\lastlogin.csv”
$Subject = “Last Login”
$Body = “Users LastLogin”
$SMTPServer = “192.168.***.**”
$SMTPPort = “587”
$password = ConvertTo-SecureString ‘My AD password’ -AsPlainText -Force
$credential = New-Object System.Management.Automation.PSCredential (‘rderousse’, $password)
[System.Net.ServicePointManager]::ServerCertificateValidationCallback = { return $true } # disable certificate
Send-MailMessage -From $From -to $To -Subject $Subject -Body $Body -SmtpServer $SMTPServer -Port $SMTPPort -UseSsl -Credential $credential -Attachments $Attachment
if($smtpport) {
Add-Type -AssemblyName System.speech
$speak = New-Object System.Speech.Synthesis.SpeechSynthesizer
$speak.Rate = 1
$speak.SetOutputToDefaultAudioDevice ;
$speak.Speak(“Your Program has completed and your email will arrive shortly”)
$speak.Dispose() }
Hi Prajwal, thankyou this was helpful. Can I suggest a small tweak to a screenshot to help people new to powershell.
In method 3 the two screen shots could build on each other.
First screenshot has
Get-ADUser -Identity “username” -Properties LastLogon
Second screen shot could reuse the above like this, repeating/building on the line above
Get-ADUser -Identity “username” -Properties LastLogon | Select-Object Name, @{N=’LastLogon’; E={[DateTime]::FromFileTime($_.LastLogon)}}
Currently the second screen shot does this
Get-ADUser -Filter {Name -eq “username”} -Properties * | Select-Object Name, @{N=’LastLogon’; E={[DateTime]::FromFileTime($_.LastLogon)}}
I just thought it may be easier for a novice to pick up by showing how one thing builds on the next.
Not a big deal… thankful for the article.
Hi, thanks for this great post.
I need to identify last logon by user with computer name and date
Ex:
user john01 last logon computername hpdesk001 06/01/2022 08:00:00
or all users last logon with computers name and date
Can you help me pls?
Happy new year.
Rgds;
Mdw
If we use “last” instead of “Last”. It shows last password set.
What about if there are multiple AD controllers? Not all data is synced between them, like last logontime. With powershell you can ask every single ad about the lastlogon attribute:
$username = Read-Host -Prompt “user login: “-Verbose
$DC_list = ((get-addomaincontroller -filter * | sort name).hostname)
$(foreach
($DC in $DC_list )
{
$user = get-aduser $username -properties LastBadPasswordAttempt,lastlogon -server $DC | select name,LastBadPasswordAttempt,lastlogon
echo “$DC `n $(w32tm /ntte $user.lastlogon)
`n $( $user.LastBadPasswordAttempt)”
})
Your code for Method 3 ignores an important condition. What happens when there is a special value to indicate that the user has never logged on?
Great tutorial Prajwal
Thank you. Simple and efficient
Thanks. Glad to hear that.